Spoofing and Phishing
Before we attempt to explain the difference between spoofing and phishing, you probably have enough experience to spot a spoofing scam since we receive so many of them. For example, a recent Yahoo spoofing email said the following:
Dear Users,
Your Account was recently signed in from a unknown Location, please verify Here for verification to avoid account locked.
Sincerely,
Yahoo
Can you guess what triggers a suspicion that this is a scam? Without clicking the hyperlink text "Here" which can cause unknown damages until the link is clicked and the malicious program is executed, a trained eye can see that there are grammatical errors such as "from a unknown" or "please verify Here for verification" or "to avoid account locked".
Also, notice the hyperlink address without clicking the link which is not related to Yahoo.
http://tinyurl.com/qzqefyt
These mistakes and observations can help detect a spoofed email which may be attempting to Phish information or achieve other malicious objectives which brings us to the difference between spoofing and phishing.
Although the terms spoofing and phishing may sound similar, phishing attacks generally use spoofing as a strategy to steal information; however, spoofing attacks are not necessarily phishing. They can be programmed to cause damage without stealing information.
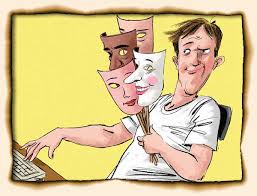
Spoofing is basically impersonating someone else in order to lure the target into doing something that they might not ordinarily and voluntarily do. For example, in the example above, Yahoo name and logo were used to gain the trust of those who own and use Yahoo email accounts. As mentioned, we don’t know whether the objective of the spoofing scam was to steal information, damage the computer, or destroy data, but someone was spoofing Yahoo to achieve a goal.
On the other hand, a phishing attack is an attack by which the sender tries to trick the target into giving up personal information resulting in financial fraud or account takeover. For example, if in the Yahoo example above, the fraudster designed the spoofed email to trick the target into giving up account details, financial data or passwords to their account, that would be considered a phishing scam which is using spoofing as a technique to achieve the phishing goals.
In summary, the difference between spoofing and phishing is that phishing scammers spoof trustworthy organizations and people in order to gain the trust of their targets and steal information; however, spoofing criminals are not necessarily trying to steal any information but may rather be trying to achieve other malicious goals such as making the target to download malicious software.








